WASM, but paranoia-friendly
Announcing 3 new projects:
- awasm: a new standard for auditable, high-security WASM packages
- awasm-compiler: an auditable js-to-wasm compiler
- awasm-noble: an ultra-fast WASM cryptography library (ChaCha/BLAKE3 at 6-10 GB/s)
First, AWASM
WASM is susceptible to covert malware injection because it’s hard to audit. Most packages are opaque, hard-to-reproduce, and async.
AWASM packages are transparent, easy-to-reproduce, and sync.
If your project follows this philosophy, feel free to call it AWASM.
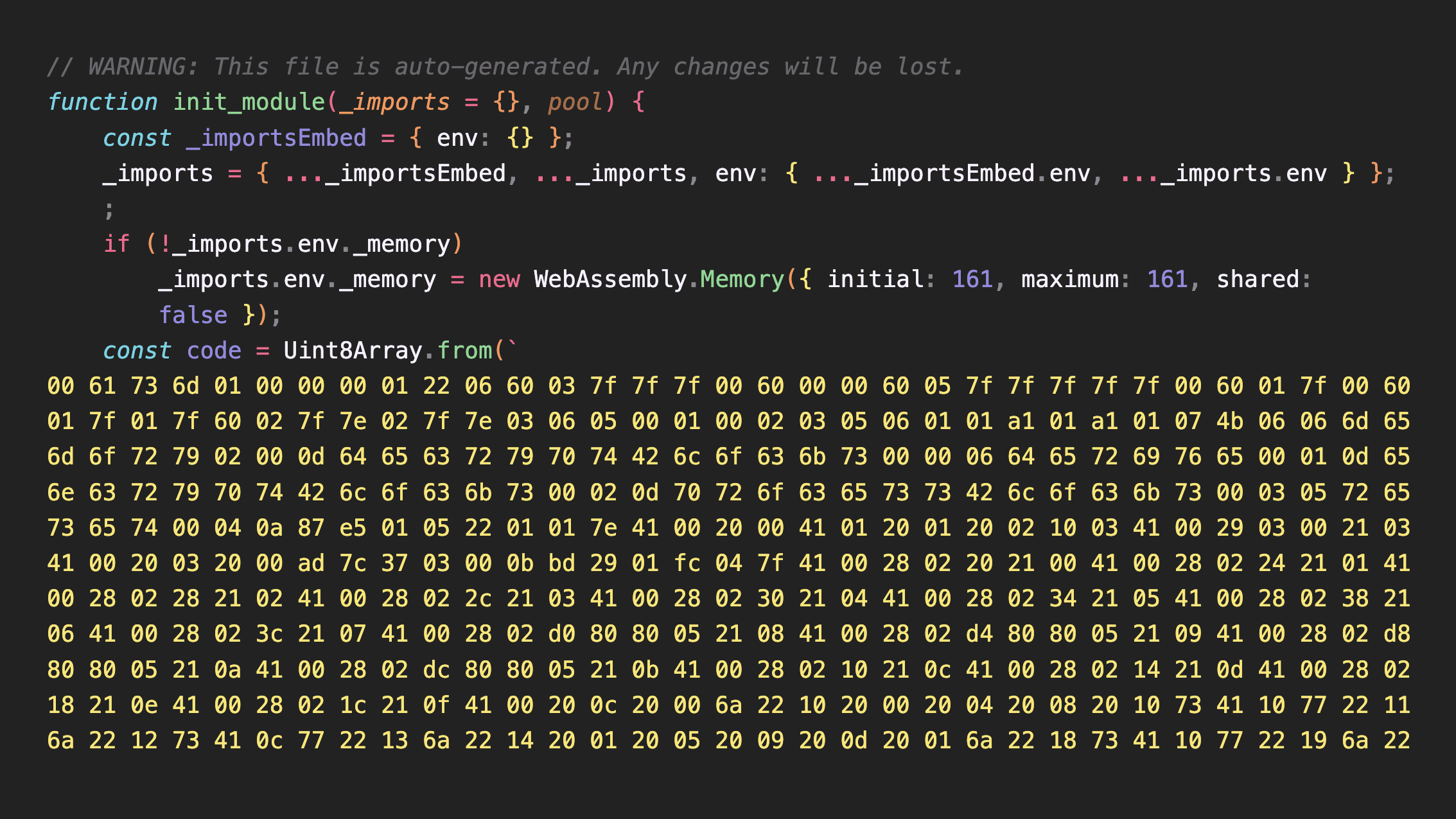
Second, awasm-compiler
JavaScript (and TypeScript) is the language of the web. It could be understood by both developers and LLMs. A custom “niche” language would struggle to match that accessibility.
awasm-compiler is 64KB JS-to-WASM compiler, built around AWASM principles.
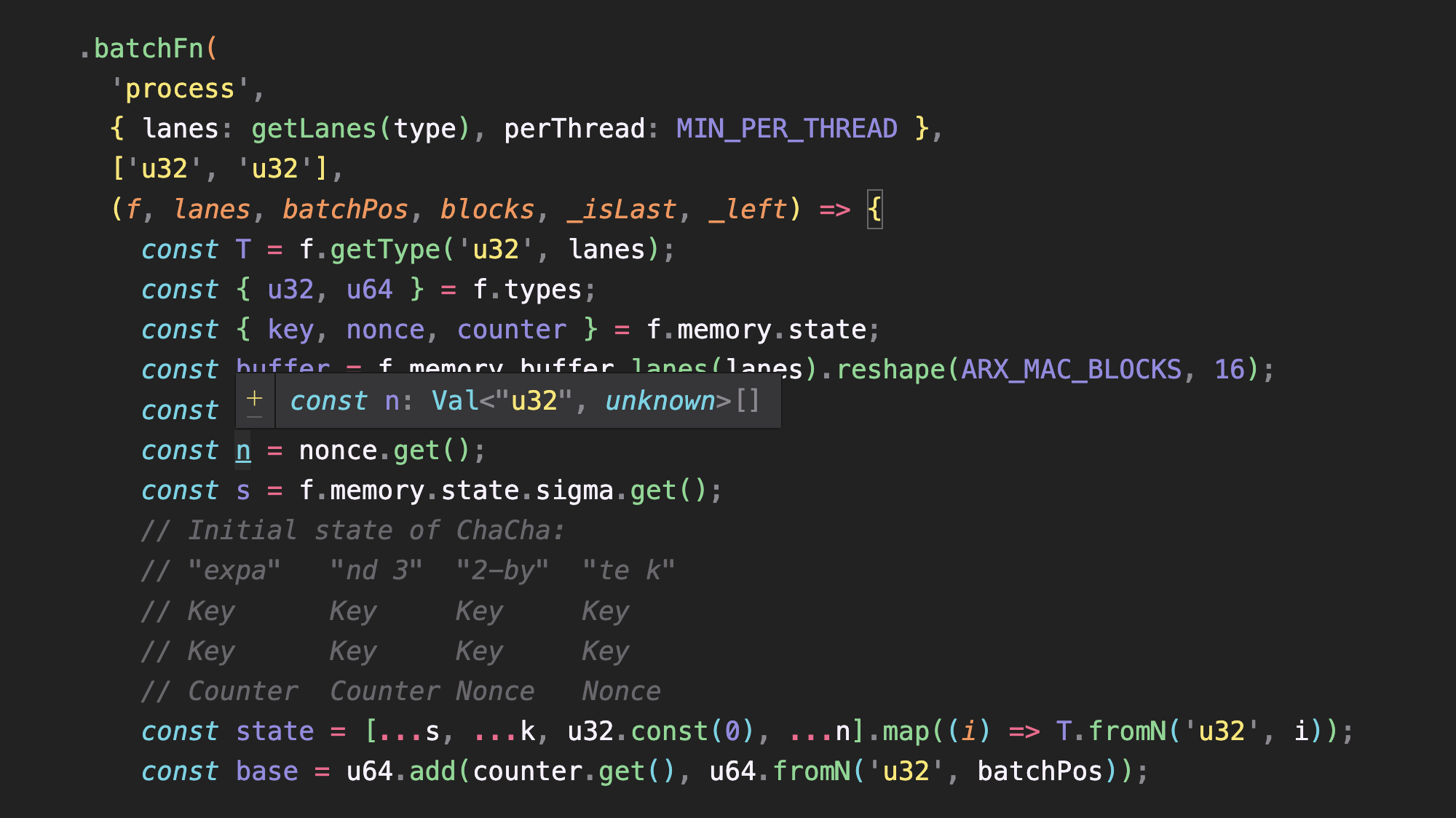
The same source code compiles to 4 different backends:
- WASM - with simd
- Threaded WASM - with web workers
- Optimized JS
- Runtime - for debugging
Optional stubs ensure non-wasm envs could run optimized JS (or even native WebCrypto) code instead of WASM.
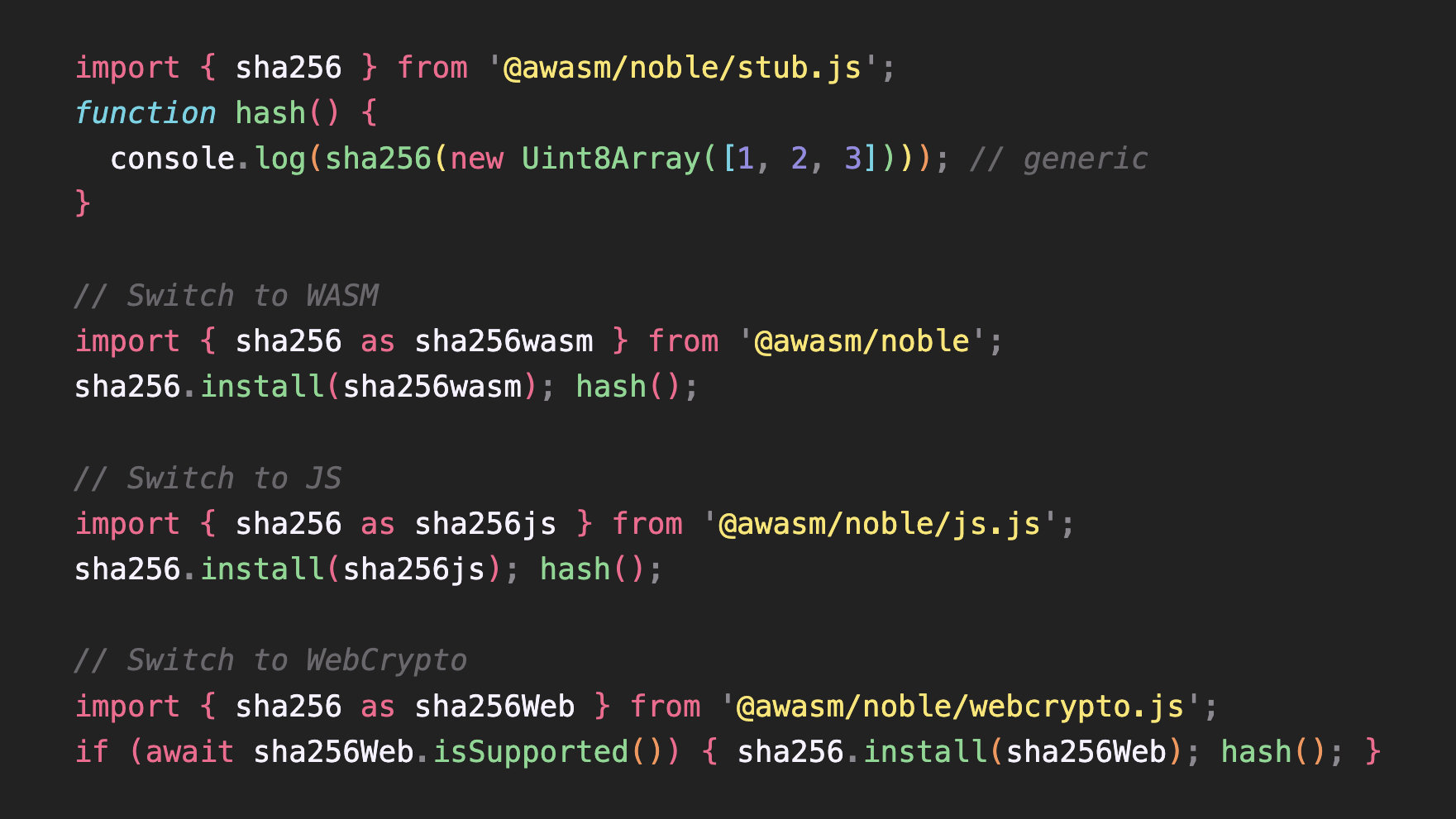
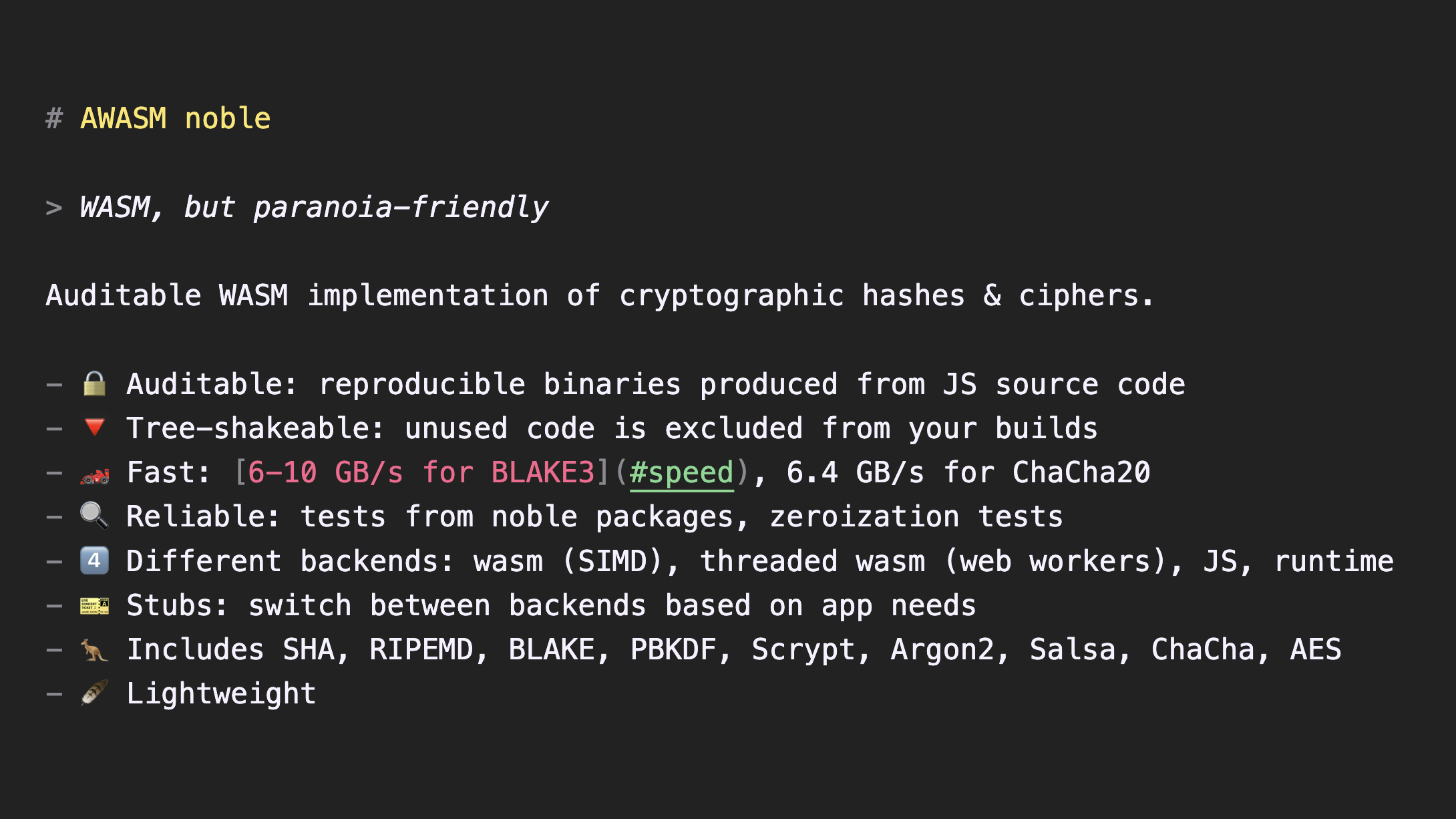
Finally, awasm-noble
A rewrite of noble cryptography - built to be the fastest WASM crypto package. It’s synchronous by default.
Performance:
- BLAKE3 (multi-input): 10.8 GB/s
- BLAKE3 (single-input): 6.3 GB/s
- ChaCha20: 6.4 GB/s
The code is available, today, on GitHub.
Links
AWASM is live now.
- awasm-noble: github, npm
- awasm-compiler: github, npm
- demo offline web app - BLAKE3 checksum calculator: b3sum.vercel.app